Name
openconnect - Connect to Cisco AnyConnect VPN
Synopsis
[https://]server[:port][/group]
Description
Sep 04, 2014 Cisco AnyConnect VPN with openvpn & openconnect I was looking for an alternative to Cisco AnyConnect VPN client for my Ubuntu box. The official client is a JAVA one and I am not interested in installing JAVA on my lean Ubuntu installation. Wrapper script for OpenConnect supporting Azure AD (SAMLv2) authentication to Cisco SSL-VPNs. Installation Using pip/pipx. A generic way that works on most 'standard' Linux distributions out of the box.
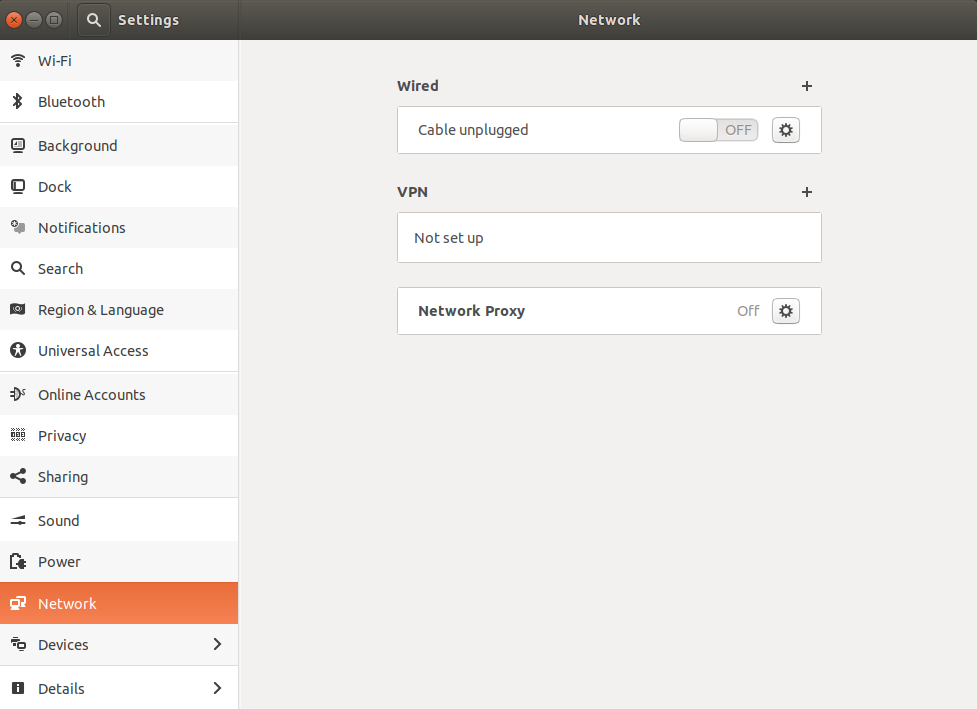
DESCRIPTION The program openconnect connects to Cisco 'AnyConnect' VPN servers, which use standard TLS and DTLS protocols for data transport. The connection happens in two phases. First there is a simple HTTPS connection over which the user authenticates somehow - by using a certificate, or password or SecurID, etc. The VPN service I've purchased uses Cisco AnyConnect, which I can't get for Linux, but the OpenConnect application is supposed to do the same thing. I've installed OpenConnect and the GUI for it. On other OS'es like Android, the VPN service simply has me link the Cisco AnyConnect client to an XML file which AnyConnect then uses to connect to. OpenConnect supports the use of HTTP and SOCKS proxies to connect to the AnyConnect service, even without using libproxy. You may wish to use libproxy if you want OpenConnect to automatically use the appropriate proxies for your environment, without having to manually give it the -proxy argument on the command line.
The program openconnect connects to Cisco 'AnyConnect' VPN servers, which use standard TLS and DTLS protocols for data transport.
The connection happens in two phases. First there is a simple HTTPS connection over which the user authenticates somehow - by using a certificate, orpassword or SecurID, etc. Having authenticated, the user is rewarded with an HTTP cookie which can be used to make the real VPN connection.
The second phase uses that cookie in an HTTPS CONNECT request, and data packets can be passed over the resulting connection. In auxiliary headersexchanged with the CONNECT request, a Session-ID and Master Secret for a DTLS connection are also exchanged, which allows data transport over UDP tooccur.
Options
--config=CONFIGFILE
Read further options from
CONFIGFILE before continuing to process options from the command line. The file should contain long-format options as wouldbe accepted on the command line, but without the two leading -- dashes. Empty lines, or lines where the first non-space character is a # character, areignored.
Any option except the config option may be specified in the file.
-b,--backgroundContinue in background after startup--pid-file=PIDFILESave the pid to PIDFILE when backgrounding-c,--certificate=CERTUse SSL client certificate CERT which may be either a file name or, if OpenConnect has been built with an appropriate version of GnuTLS, a PKCS#11URL.-e,--cert-expire-warning=DAYSGive a warning when SSL client certificate has DAYS left before expiry-k,--sslkey=KEYUse SSL private key KEY which may be either a file name or, if OpenConnect has been built with an appropriate version of GnuTLS, a PKCS#11URL.-C,--cookie=COOKIEUse WebVPN cookie COOKIE--cookie-on-stdinRead cookie from standard input-d,--deflateEnable compression (default)-D,--no-deflateDisable compression--force-dpd=INTERVALUse INTERVAL as minimum Dead Peer Detection interval for CSTP and DTLS, forcing use of DPD even when the server doesn't request it.-g,--usergroup=GROUPUse GROUP as login UserGroup-h,--helpDisplay help text-i,--interface=IFNAMEUse IFNAME for tunnel interface-l,--syslogUse syslog for progress messages-U,--setuid=USERDrop privileges after connecting, to become user USER--csd-user=USERDrop privileges during CSD (Cisco Secure Desktop) script execution.--csd-wrapper=SCRIPTRun SCRIPT instead of the CSD (Cisco Secure Desktop) script.-m,--mtu=MTURequest MTU from server as the MTU of the tunnel.--basemtu=MTUIndicate MTU as the path MTU between client and server on the unencrypted network. Newer servers will automatically calculate the MTU to be used onthe tunnel from this value.-p,--key-password=PASSProvide passphrase for certificate file, or SRK (System Root Key) PIN for TPM-P,--proxy=PROXYURLUse HTTP or SOCKS proxy for connection--no-proxyDisable use of proxy --libproxyUse libproxy to configure proxy automatically (when built with libproxy support)--key-password-from-fsidPassphrase for certificate file is automatically generated from the fsid of the file system on which it is stored. The fsid is obtained fromthe statvfs(2) or statfs(2) system call, depending on the operating system. On a Linux or similar system with GNU coreutils, the fsid usedby this option should be equal to the output of the command: stat --file-system --printf=%in $CERTIFICATE It is not the same as the 128-bit UUID of the filesystem.-q,--quietLess output-Q,--queue-len=LENSet packet queue limit to LEN pkts-s,--script=SCRIPTInvoke SCRIPT to configure the network after connection. Without this, routing and name service are unlikely to work correctly. The script isexpected to be compatible with the vpnc-script which is shipped with the 'vpnc' VPN client. Seehttp://www.infradead.org/openconnect/vpnc-script.html for more information. This version of OpenConnect is configured to use/etc/vpnc/vpnc-script by default.-S,--script-tunPass traffic to 'script' program over a UNIX socket, instead of to a kernel tun/tap device. This allows the VPN IP traffic to be handled entirely inuserspace, for example by a program which uses lwIP to provide SOCKS access into the VPN.
--libproxyUse libproxy to configure proxy automatically (when built with libproxy support)--key-password-from-fsidPassphrase for certificate file is automatically generated from the fsid of the file system on which it is stored. The fsid is obtained fromthe statvfs(2) or statfs(2) system call, depending on the operating system. On a Linux or similar system with GNU coreutils, the fsid usedby this option should be equal to the output of the command: stat --file-system --printf=%in $CERTIFICATE It is not the same as the 128-bit UUID of the filesystem.-q,--quietLess output-Q,--queue-len=LENSet packet queue limit to LEN pkts-s,--script=SCRIPTInvoke SCRIPT to configure the network after connection. Without this, routing and name service are unlikely to work correctly. The script isexpected to be compatible with the vpnc-script which is shipped with the 'vpnc' VPN client. Seehttp://www.infradead.org/openconnect/vpnc-script.html for more information. This version of OpenConnect is configured to use/etc/vpnc/vpnc-script by default.-S,--script-tunPass traffic to 'script' program over a UNIX socket, instead of to a kernel tun/tap device. This allows the VPN IP traffic to be handled entirely inuserspace, for example by a program which uses lwIP to provide SOCKS access into the VPN.Anyconnect Vs Openconnect
-u,--user=NAMESet login username to NAME-V,--versionReport version number-v,--verboseMore output-x,--xmlconfig=CONFIGXML config file--authgroup=GROUPChoose authentication login selection--authentiateAuthenticate only, and output the information needed to make the connection a form which can be used to set shell environment variables. When invoked withthis option, openconnect will not make the connection, but if successful will output something like the following to stdout:Thus, you can invoke openconnect as a non-privileged user (with access to the user's PKCS#11 tokens, etc.) for authentication, and then invokeopenconnect separately to make the actual connection as root: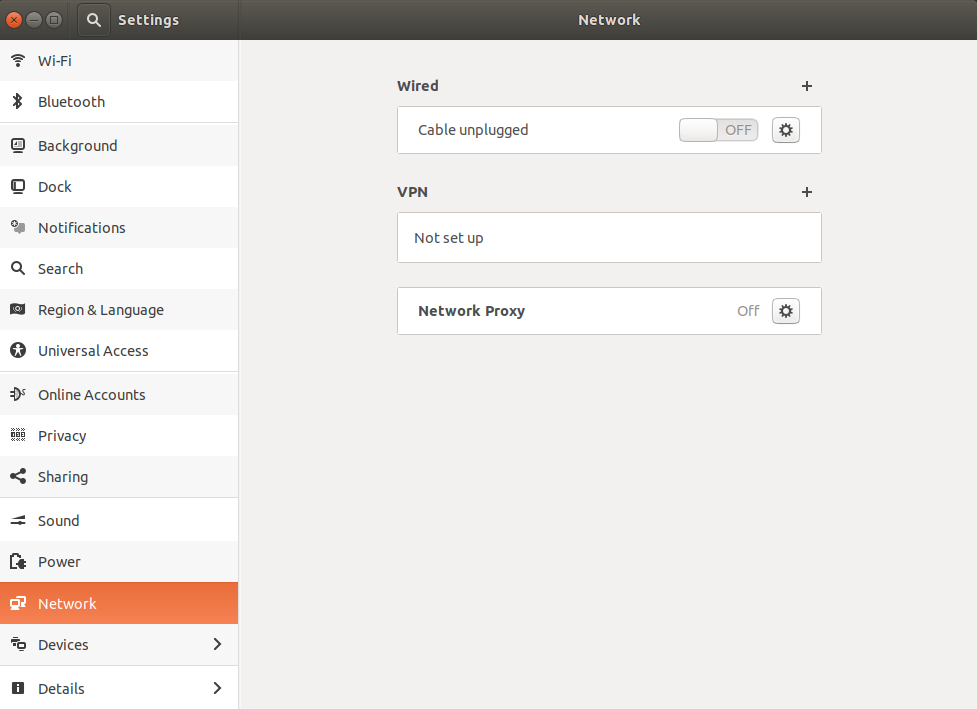
 --cookieonlyFetch webvpn cookie only; don't connect--printcookie
--cookieonlyFetch webvpn cookie only; don't connect--printcookieOpenconnect Anyconnect Profile
Print webvpn cookie before connecting--cafile=FILECert file for server verification--disable-ipv6Do not advertise IPv6 capability to server--dtls-ciphers=LISTSet OpenSSL ciphers to support for DTLS--no-cert-checkDo not require server SSL certificate to be valid. Checks will still happen and failures will cause a warning message, but the connection will continueanyway. You should not need to use this option - if your servers have SSL certificates which are not signed by a trusted Certificate Authority, you can stilladd them (or your private CA) to a local file and use that file with the --cafile option.--no-dtlsDisable DTLS--no-http-keepaliveVersion 8.2.2.5 of the Cisco ASA software has a bug where it will forget the client's SSL certificate when HTTP connections are being re-used for multiplerequests. So far, this has only been seen on the initial connection, where the server gives an HTTP/1.0 redirect response with an explicit
Connection:Keep-Alive directive. OpenConnect as of v2.22 has an unconditional workaround for this, which is never to obey that directive after an HTTP/1.0 response.
However, Cisco's support team has failed to give any competent response to the bug report and we don't know under what other circumstances their bug mightmanifest itself. So this option exists to disable ALL re-use of HTTP sessions and cause a new connection to be made for each request. If your server seems notto be recognising your certificate, try this option. If it makes a difference, please report this information to theopenconnect-devel@lists.infradead.org mailing list.
--no-passwdNever attempt password (or SecurID) authentication.--non-interDo not expect user input; exit if it is required.--passwd-on-stdinRead password from standard input--reconnect-timeoutKeep reconnect attempts until so much seconds are elapsed. The default timeout is 300 seconds, which means that openconnect can recover VPN connection aftera temporary network down time of 300 seconds.--servercert=SHA1Accept server's SSL certificate only if its fingerprint matches SHA1.--useragent=STRINGUse STRING as 'User-Agent:' field value in HTTP header. (e.g. --useragent 'Cisco AnyConnect VPN Agent for Windows 2.2.0133')--dtls-local-port=PORTUse PORT as the local port for DTLS datagramsLimitations
Note that although IPv6 has been tested on all platforms on which openconnect is known to run, it depends on a suitable vpnc-script toconfigure the network. The standard vpnc-script shipped with vpnc 0.5.3 is not capable of setting up IPv6 routes; the one fromgit://git.infradead.org/users/dwmw2/vpnc-scripts.git will be required.
Authors
Anyconnect Openconnect Login
David Woodhouse <dwmw2@infradead.org>