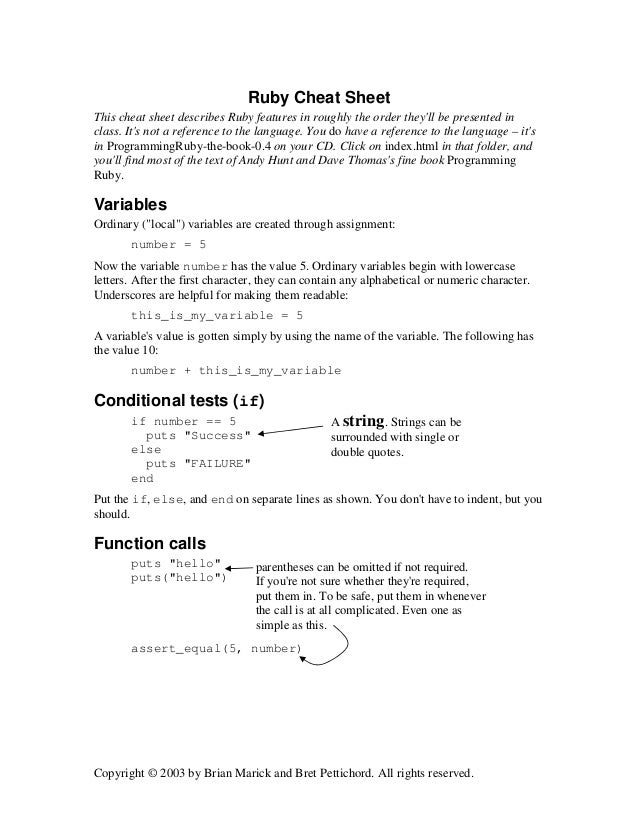
Ruby Cheatsheet
If you’re lucky enough to find a command execution vulnerability during a penetration test, pretty soon afterwards you’ll probably want an interactive shell.
- Ruby Hashes Cheat Sheet.
- In Ruby, just as methods can be overriden and advised,classesare open: They can be extendedanytime. # Open up existing class and add a method. ClassFixnum defmytimes;self.downto1doyieldendend end 3.mytimesdoputs'neato'end #.
- The Ultimate Docker Cheat Sheet Docker - Beginners Intermediate Advanced View on GitHub Join Slack The Ultimate Docker Cheat Sheet. Complete Docker CLI. Container Management CLIs. Inspecting The Container. Interacting with Container. Image Management Commands. Image Transfer Comnands. Builder Main Commands.
Ruby cheatsheet This is a cheatsheet for Ruby beginners and contains links to resources and some simple examples to get started with Ruby. Denial of Service Cheat Sheet¶ Introduction¶. This sheet is focused on providing an overall, common overview with an informative, straight to the point guidance to propose angles on how to battle denial of service (DoS) attacks on different layers.
If it’s not possible to add a new account / SSH key / .rhosts file and just log in, your next step is likely to be either trowing back a reverse shell or binding a shell to a TCP port. This page deals with the former.
Your options for creating a reverse shell are limited by the scripting languages installed on the target system – though you could probably upload a binary program too if you’re suitably well prepared.
The examples shown are tailored to Unix-like systems. Some of the examples below should also work on Windows if you use substitute “/bin/sh -i” with “cmd.exe”.
Each of the methods below is aimed to be a one-liner that you can copy/paste. As such they’re quite short lines, but not very readable.
Bash
Some versions of bash can send you a reverse shell (this was tested on Ubuntu 10.10):
PERL
Here’s a shorter, feature-free version of the perl-reverse-shell:
There’s also an alternative PERL revere shell here.
Python
This was tested under Linux / Python 2.7:
PHP
This code assumes that the TCP connection uses file descriptor 3. This worked on my test system. If it doesn’t work, try 4, 5, 6…
If you want a .php file to upload, see the more featureful and robust php-reverse-shell.
Ruby
Netcat
Netcat is rarely present on production systems and even if it is there are several version of netcat, some of which don’t support the -e option.
If you have the wrong version of netcat installed, Jeff Price points out here that you might still be able to get your reverse shell back like this:
Java
[Untested submission from anonymous reader]
xterm
One of the simplest forms of reverse shell is an xterm session. The following command should be run on the server. It will try to connect back to you (10.0.0.1) on TCP port 6001.
To catch the incoming xterm, start an X-Server (:1 – which listens on TCP port 6001). One way to do this is with Xnest (to be run on your system):
You’ll need to authorise the target to connect to you (command also run on your host):
Further Reading
Ruby Programming For Kids
Also check out Bernardo’s Reverse Shell One-Liners. He has some alternative approaches and doesn’t rely on /bin/sh for his Ruby reverse shell.
There’s a reverse shell written in gawk over here. Gawk is not something that I’ve ever used myself. However, it seems to get installed by default quite often, so is exactly the sort of language pentesters might want to use for reverse shells.
Tags: bash, cheatsheet, netcat, pentest, perl, php, python, reverseshell, ruby, xterm
Posted in Shells
Pokemon Ruby Gameshark Codes
- PDF Link: cheatsheet-ruby-A4.pdf, Category: languages
- Blog URL: https://cheatsheet.dennyzhang.com/cheatsheet-ruby-A4
- Related posts: Golang CheatSheet, Python CheatSheet, #denny-cheatsheets
File me Issues or star this repo.
1.1 Summary
| Name | Comment |
|---|---|
| Check syntax | ruby -c my.rb |
| Generate random key | r = Random.new, r.rand(10...42) |
| Install ruby 2.4 | GitHub: Ubuntu install ruby 2.4 |
| Install package with specific version | gem install rubocop -v '0.44.1' |
| Install package with a range of versions | gem install rails -v '~>4.0.0' |
| Install package with a range of versions | gem install rails -v '>3.1, <4.1' |
| Get RubyGem env | gem env |
| Check whether variable is nil | if value.nil? |
| Run system command | system('commandhere') |
| Run bash command | stdin, stdout, stderr = Open3.popen3('ls .') |
1.2 List
| Name | Comment |
|---|---|
| Check existence | [‘Cat’, ‘Dog’, ‘Bird’].include? ‘Dog’ |
| Find item | l1.find_index(x) |
| Remove item from list | l1.delete_at(2) |
| Remove duplicate entries | [1,2,2,1,4,4,5,6,7,8,5,6].uniq |
| Deep copy a list | l1=l.dup |

1.3 String
| Name | Comment |
|---|---|
| Substring | string[1..3] |
| Search substring | “option=name=bob”.index(“name”) |
| Replace | “Welcome to PHP Essentials!”.gsub(“PHP”, “Ruby”) |
| Remove trailing comma | “ab;123;”.chomp(“;”) |
| Strip whitespace | host = host.strip() |
1.4 Integer
1.5 Conversion
| Name | Comment |
|---|---|
| Convert string to int | “14”.toi, “1,112”.delete(‘,’).toi |
| Round float to 2 digits | (5.65235534).round(2) |
| Format datetime | puts time.strftime('%Y-%m-%d %H:%M:%S') |
1.6 Dict & Set
1.7 File
| Name | Comment |
|---|---|
| Check whether directory exist | File.directory?('xxx') |
| Check whether files exist | File.file?('hello.rb') |
| Read file to string | contents = File.read('filename') |
- Write to file
1.8 Code Snippets
- Get ip from eth0
- Get hostname
- Get hostname from ip
1.9 More Resources
